UK Cyber Security and Resilience Bill: Why MSPs Are About to Become the Front Line
The UK just drew a line in the sand. The Cyber Security and Resilience Bill — currently grinding through Parliament — is the most significant overhaul of British cyber regulation since 2018. And the headline isn’t about firewalls or encryption. It’s about Managed Service Providers.
For the first time, the companies that manage IT systems for thousands of other organisations are being dragged into regulatory scope. Not because someone woke up worried about best practice — but because the attacks keep coming, and the gaps keep getting exploited.
The MSP Problem Nobody Wanted to Address
Here’s the uncomfortable truth: until this Bill, MSPs were essentially invisible to UK cyber law. These are companies with privileged access to their clients’ networks, systems, and data — the digital keys to thousands of businesses — and they operated without a single regulatory obligation around cybersecurity.
That’s not a gap. That’s a chasm.
The definition is specific: a “Relevant Managed Service Provider” (RMSP) provides ongoing, contracted IT management — think help desk, network monitoring, cloud administration, managed security — and connects to customer systems. Micro and small enterprises are exempted. Medium and large MSPs are not. The estimated impact? Between 900 and 1,100 additional firms suddenly finding themselves under regulatory scrutiny.
The Information Commissioner will act as their regulator. And the IC has already signalled support, calling the expansion “a natural progression.”
But “natural progression” undersells what actually happened. What happened was a series of catastrophic breaches that proved MSPs were the softest target in the supply chain.
Operation Cloud Hopper and the MOD Breach: Why MSPs Matter
The case for regulating MSPs didn’t come from a think tank paper. It came from body count.
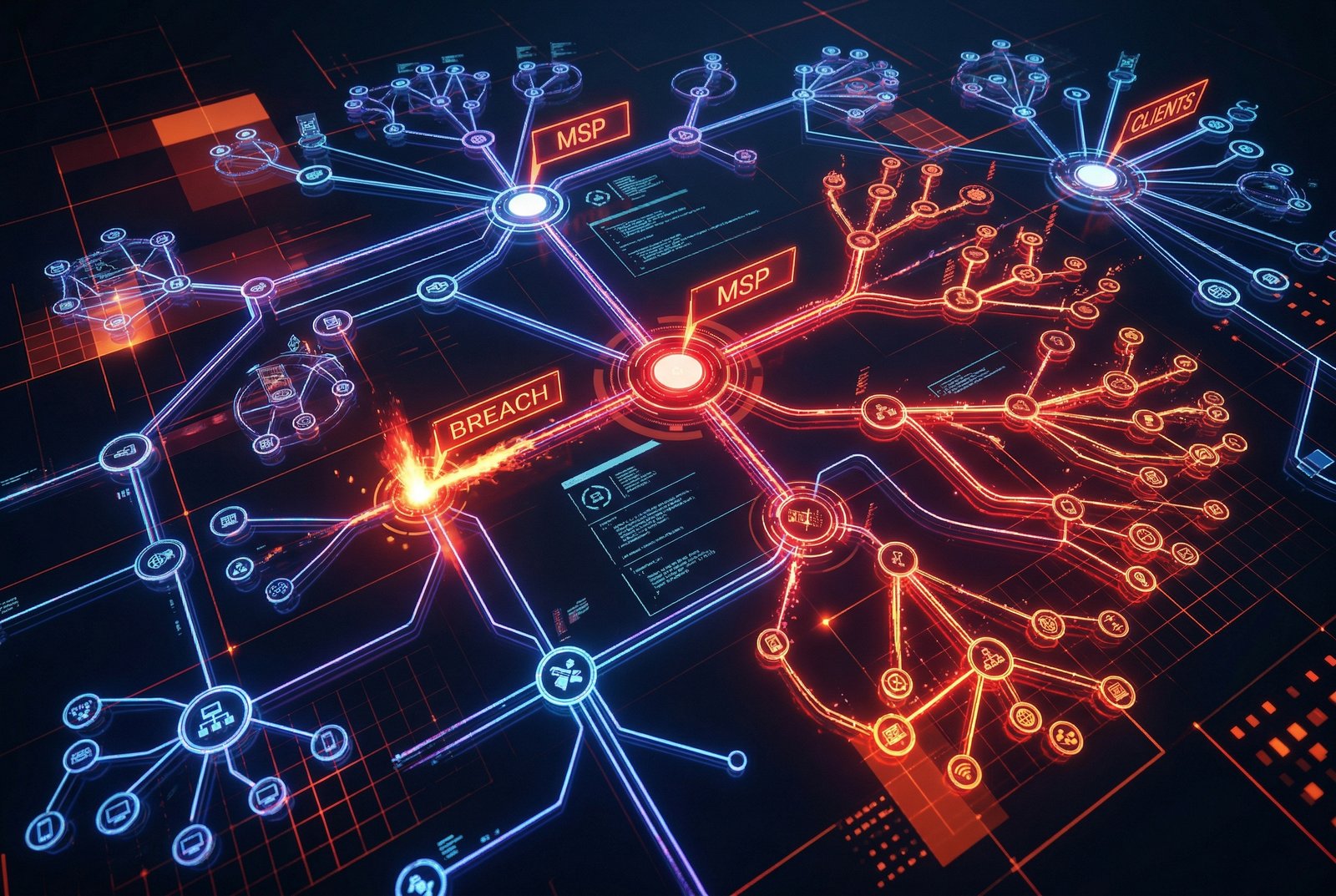
Operation Cloud Hopper — a state-sponsored campaign attributed to Chinese threat actors — systematically compromised MSPs across the globe to gain access to their clients’ networks. One MSP breach, dozens of downstream victims. The attackers didn’t need to hack each target individually. They hacked the company that managed all of them.
Then came May 2024. Hackers compromised an MSP’s network and walked away with records belonging to approximately 270,000 military personnel — the Ministry of Defence payroll breach. Not a sophisticated zero-day. Not an exotic attack vector. A supply chain compromise through a managed service provider that had no regulatory obligation to meet baseline security standards.
The NCSC has been managing one significant cyber incident every two days on average. In the 12 months to August 2025, the UK saw 211 nationally significant cyber incidents — a 137% increase from the 89 recorded the previous year. The country is now experiencing what the NCSC’s own Annual Review described as four “nationally significant” cyber attacks per week.
The MSP-shaped hole in UK regulation wasn’t theoretical. It was being exploited constantly.
What the Bill Actually Changes

The Cyber Security and Resilience Bill amends the Network and Information Systems (NIS) Regulations 2018 — the framework that currently governs cyber security for essential services and limited digital services. The original NIS regime was based on the EU NIS Directive and was always designed to be updated. It just took eight years and a pile of breach reports to get there.
New scope: Beyond MSPs, the Bill brings data centres (already designated as Critical National Infrastructure since September 2024) and “large load controllers” — essentially smart appliance managers — into regulatory scope. It also creates a new power to designate third-party suppliers whose disruption would cause “considerable economic or societal consequences.”
Incident reporting: The current regime has vague, sector-dependent timelines. The Bill introduces mandatory dual reporting: 24-hour early notification followed by a 72-hour detailed incident report. No ambiguity, no discretion.
Regulator powers: Competent authorities gain enhanced investigatory powers, the ability to conduct proactive vulnerability assessments, and cost recovery mechanisms. They can also require information about supply chain dependencies — a direct response to the MSP problem.
Scope expansion without new legislation: Perhaps the most consequential provision. The Secretary of State gains the power to expand the regulatory scope via secondary legislation. No more waiting for a new Bill to go through Parliament when a new type of threat emerges. The regime becomes dynamic.
Penalties: The existing maximum — greater of £17 million or 4% of global annual turnover — remains. But the Bill adds new teeth: £100,000 per day for continuing non-compliance, and up to £10 million (or £50,000/day) for failing to comply with information notices. These are GDPR-level enforcement tools.
The Supply Chain Angle
The Bill doesn’t just regulate MSPs directly. It introduces a designated critical supplier regime that targets the broader supply chain.
A supplier can be designated if they provide goods or services directly to an Operator of Essential Services, Relevant Digital Service Provider, or Relevant Managed Service Provider; depend on network and information systems; and have a credible possibility of disrupting service provision with considerable economic or societal consequences.
Designated suppliers face fundamental security requirements, incident reporting obligations, and proportionate measures based on their risk profile. The details will be set through secondary legislation, but the framework is clear: if you’re in the supply chain of critical infrastructure, you’re potentially in scope.
This is a significant philosophical shift. The NIS 2018 focused on the operators themselves — the energy companies, the water utilities, the transport networks. The Bill recognises that the real vulnerability isn’t always at the top of the chain. It’s in the middle, where a single compromised service provider can cascade disruption across entire sectors.
💡 £27 billion — the estimated annual cost of cyber attacks to the UK economy. The average cost of a data breach in the UK now sits at approximately £3.6 million. The Synnovis NHS pathology attack alone cost £32.7 million.
How It Compares to the EU’s NIS2
The UK’s approach is sometimes described as “NIS2-lite” — and that’s not entirely wrong, but it misses important nuances.
The EU’s NIS2 Directive, which came into force in October 2024, is broader in scope (covering more entity types and sectors), more prescriptive in its security requirements, and imposes stricter penalty frameworks in some respects. It also applies to a wider range of medium and large enterprises across 18 sectors.
The UK Bill is deliberately more flexible. Rather than naming every sector and entity type in primary legislation, it creates a framework that can be expanded dynamically. The Secretary of State can bring new sectors or entity types into scope through secondary legislation as threats evolve.
This flexibility has trade-offs. It means faster response to emerging threats — no more eight-year gaps between regulatory updates. But it also means less certainty for businesses about what might come next. Industry groups have expressed concern about the “secondary legislation uncertainty” — the key details about exact security standards and designation criteria are deferred to future regulation.
The UK has also diverged from the EU on regulatory structure. The EU moved toward stronger centralised coordination through ENISA. The UK is maintaining its federated model with 12 sector-specific regulators. Some industry voices have called for a single unified cyber regulator, but the government has defended the sectoral approach as more responsive to sector-specific risks.
Who’s Missing — And Why That Matters
Here’s the uncomfortable part that doesn’t make it into government press releases.
Marks & Spencer. Jaguar Land Rover. Both hit by major cyber attacks in 2025. Neither operates in a sector covered by the Bill.
The retail sector isn’t in scope. Automotive manufacturing isn’t in scope. When the NCSC talks about four nationally significant attacks per week, a meaningful chunk of those are hitting organisations that sit entirely outside this regulatory framework.
The Secretary of State’s new power to expand scope via secondary legislation is partly a response to this — the government is acknowledging that it can’t predict which sectors will be targeted next. But as of today, the Bill’s immediate coverage leaves significant parts of the UK economy exposed.
There’s also the question of enforcement reality versus regulatory ambition. The NIS 2018 already had penalties of up to £17 million or 4% of turnover. They were rarely used. Adding £100,000/day fines sounds impressive on paper. Whether regulators have the resources and willingness to actually impose them is another question entirely.
What MSPs Need to Do Now

If you’re an MSP reading this, the regulatory train has left the station. The Bill is progressing through Parliament with cross-party support. It’s expected to become law in 2026, with secondary legislation setting specific technical standards to follow.
Immediate steps:
- Assess your scope: Are you medium or large? Do you provide ongoing contracted IT management with access to customer systems? If yes, you’re likely in scope.
- Start documenting security measures: The Bill requires “appropriate and proportionate” security measures. Regulators will expect evidence, not assertions.
- Build incident reporting capability: 24-hour early notification plus 72-hour detailed reporting is a tight timeline. You need processes, not just intentions.
- Map your supply chain: The designated critical supplier regime means your own suppliers could be regulated. You need visibility into your dependencies.
- Engage with the IC: The Information Commissioner will be your regulator. Understanding their expectations early is cheaper than learning through enforcement.
The Clifford Chance analysis puts it bluntly: MSPs need to start preparing now, because the secondary legislation will arrive faster than most expect.
The Broader Picture
Jon Ellison, NCSC Director of National Resilience, called the Bill “a landmark moment tackling the growing threat to the UK’s critical systems” and “a crucial step towards a more comprehensive regulatory framework.”
He’s right — but the word “step” is doing heavy lifting. This Bill is a foundation, not a finish line. It fixes the most obvious gap (MSPs), creates a more flexible regulatory architecture, and gives regulators sharper tools. It does not, and cannot, address every sector or every threat vector.
The real test will be execution. Will the secondary legislation arrive with clear, actionable standards — or vague principles that create compliance confusion? Will regulators actually use the enhanced powers — or will the £100,000/day fines sit unused like their predecessors? Will the Secretary of State’s dynamic scope expansion power be exercised proactively — or only after the next major breach forces it?
The UK cyber security posture is improving. 211 nationally significant incidents in a year — up 137% — is partly a reflection of better detection, not just more attacks. The NCSC is more active, more visible, and more resourced than at any point in its history. The Cyber Security and Resilience Bill is the legislative backing for what the NCSC has been doing operationally.
But legislation is only as effective as its implementation. And in cybersecurity, implementation is everything.
What Happens Next
The Bill is currently progressing through Parliament, having had its second reading on 6 January 2026. It’s expected to become law later this year, with secondary legislation to follow.
For MSPs, the compliance clock starts when the secondary legislation is published — not when the Bill receives Royal Assent. Smart operators won’t wait. They’ll start preparing now, because the threat environment isn’t pausing for parliamentary procedure.
For the broader UK economy, the Bill signals that the government is moving from a posture of “encouraging good practice” to one of “mandating minimum standards.” Whether those minimum standards are high enough — and whether they’re enforced with sufficient rigour — will determine whether this landmark moment translates into actual resilience.
The stakes are clear. £27 billion annually in cyber attack costs. Four nationally significant attacks per week. 211 major incidents in twelve months. The UK can’t afford to wait for perfect regulation. It needs workable regulation, enforced consistently, updated dynamically.
The Cyber Security and Resilience Bill is that bet. We’re about to find out if it pays off.
Related Reading
- UK FCA Crypto Licensing Regime: October 2027 Deadline and £150K Minimum Capital — The FCA’s parallel regulatory push for crypto firms, with similar supply chain and compliance implications
- Why 93% of UK Critical National Infrastructure Providers Have Been Successfully Attacked — The incident response gaps that make this legislation urgent
- UK Postponing AI Compliance Deadlines: Pulling Back From Strict Regulation — How the UK’s lighter-touch approach to AI regulation contrasts with its hardening stance on cyber
Sources
- UK Government Bill Summary
- UK Parliament Bill Page
- NCSC Policy Statement
- House of Commons Library Briefing
- GOV.UK MSP Factsheet
- Clifford Chance Analysis
- SysGroup MSP Analysis
- Crowell & Moring Analysis
- TLT LLP Analysis
- Local Government Association Briefing
- Security Journal UK
- Infosecurity Magazine — Key Provisions
- Gowling WLG Analysis
- ICO Response
- ISC2 Roundtable
- Infosecurity Magazine — Parliament Asks Industry
- GOV.UK Economic Impact Summary
- NCSC Annual Review
- techUK Economic Study
- ANSecurity Statistics

